1. [PDF] Cyber Awareness Challenge 2022 Information Security
Spillage occurs when information is “spilled” from a higher classification ... • Refer any inquiries to your organization's public affairs office.
2. [PDF] Cyber Awareness Challenge 2020 Information Security
Spillage occurs when information is “spilled” from a higher classification or protection level to a lower classification or protection level. Spillage can be ...
3. Cyber Awareness Challenge 2023 Answers | Exams Information ...
(Spillage) What should you do if a reporter asks you about potentially classified information on the web? Refer the reporter to your organization's public ...
Download Exams - Cyber Awareness Challenge 2023 Answers | Harvard University | Cyber Awareness Challenge 2023 Answers

4. DOD | CYBER HYGIENE | Information security helps protect from ...
16 jun 2023 · Spillage occurs when information is “spilled” from a higher classification or protection level to a lower classification or protection level.
This article focuses on the different designation for unclassified and classified information.

5. Defining Spillage in Cyber Awareness - Sandra Estok
13 nov 2023 · Spillage, in the context of cyber awareness, refers to the unauthorized or accidental exposure of sensitive information beyond its intended ...
Explore the Impact of Spillage in Cyber Awareness Efforts. Learn How to Prevent Data Leaks.
6. DOD CYBER AWARENESS CHALLENGE KNOWLEDGE ...
Inquiry from a reporter...?: Refer to public affairs 6. What does spillage refer to?: Information improperly moved from higher to lower protection level 7.
Download Exams - DOD CYBER AWARENESS CHALLENGE KNOWLEDGE CHECK 2024 ASSESSMENT QUESTIONS WITH ANSWERS | Harvard University | DOD CYBER AWARENESS CHALLENGE KNOWLEDGE CHECK 2024 ASSESSMENT QUESTIONS WITH ANSWERS

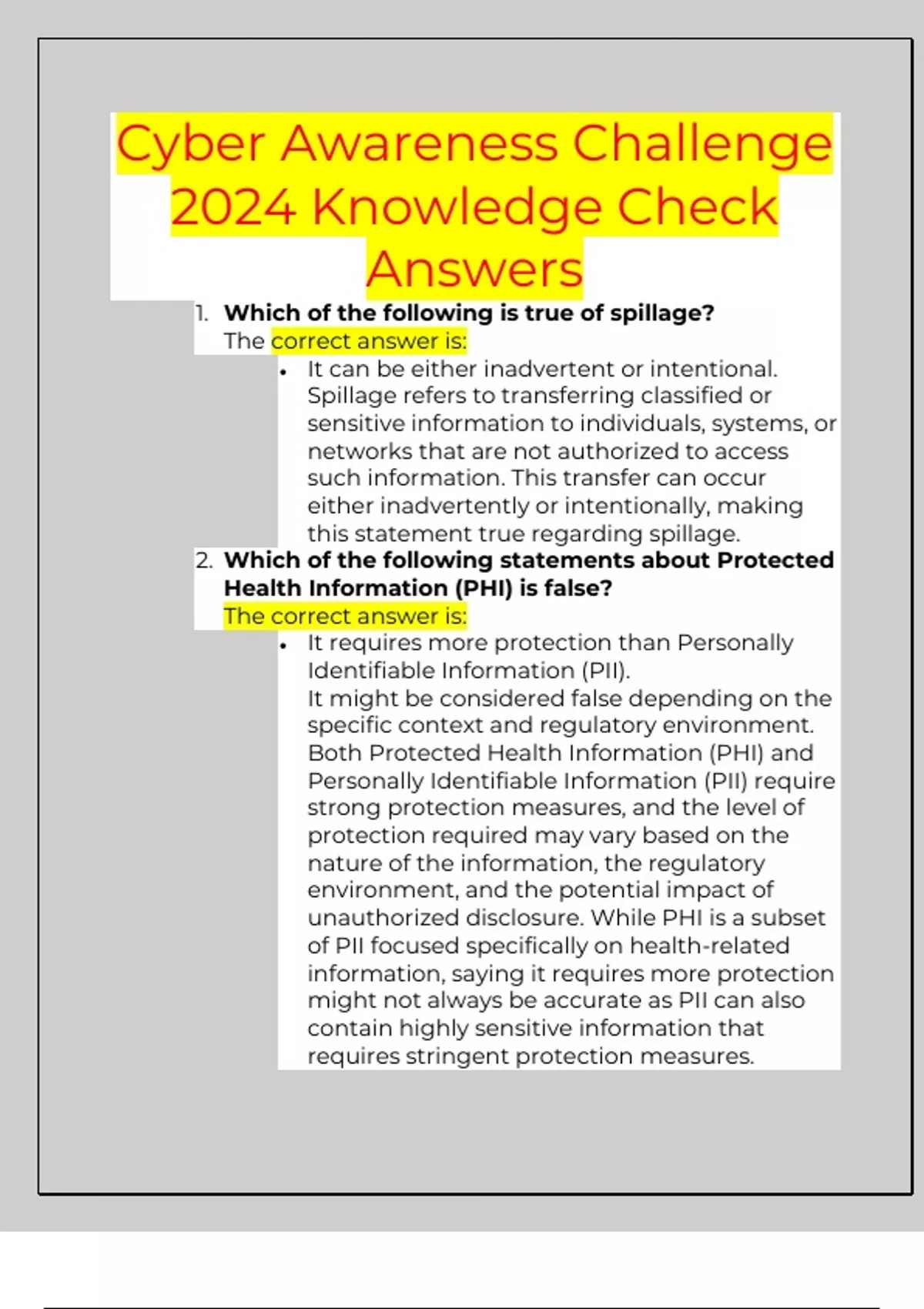
7. Cyber Awareness Challenge 2024 Knowledge Check Answers 100 ...
... would be to: • Delete the message. It's advisable not to engage with ... Spillage refers to transferring classified or sensitive information to ...
ot authorized to access such information. This transfer can occur either inadvertently or intentionally, making this statement true regarding spillage. 2. Which of the following statements about Protected Health Information (PHI) is false? The correct answer is: • It requires more protection than Personally Identifiable Information (PII). It might be considered false depending on the specific context and regulatory environment. Both Protected Health Information (PHI) and Personally Identifiable Information (PII) require strong protection measures, and the level of protection required may vary based on the nature of the information, the regulatory environment, and the potential impact of unauthorized disclosure. While PHI is a subset of PII focused specifically on health-related information, saying it requires more protection might not always be accurate as PII can also contain highly sensitive information that requires stringent protection measures. 3. On your home computer, how can you best establish passwords when creating separate user accounts? The best practice among the provided options for establishing passwords when creating separate user accounts on your home computer is: • Have each user create their own, strong password. This approach promotes good security hygiene by ensuring that each user has a unique, strong password, which can help prevent unauthorized access and protect the privacy and data of each us...
8. Dod cyber awareness challenge knowledge check 2023 - Studypool
correct answers Refer to public affairs What does spillage refer to? correct answers Information improperly moved from higher to lower protection level ...
Which of the following may help to prevent spillage? correct answers Follow procedures fortransferring data to and from outside agency and non-Government networks
